If you needed any evidence that ransomware makers have no shame, here it is. The creators of one ransomware strain set up a ‘technical support’ page for their victims—and the messages they have left are truly distressing.
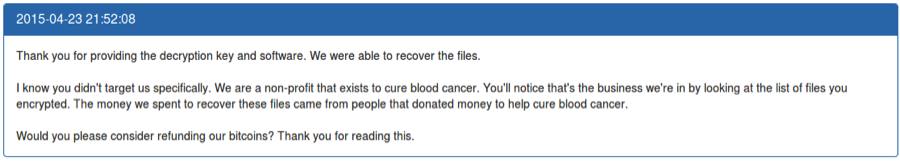
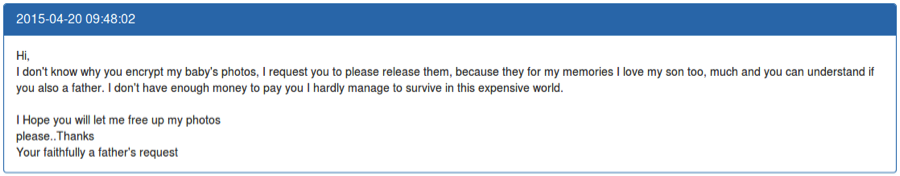
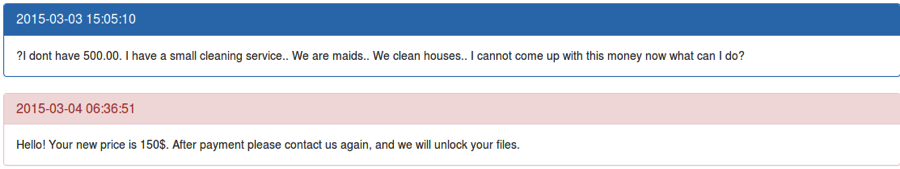
A father with little cash, robbed of his baby’s pictures; a non-profit that raises money for curing blood cancer, pleading for a refund; a housecleaning business set up by maids who can’t afford to pay the ransom.
The site not only shows victims pleading directly with the ransomware makers. It also shows an exceptionally rare event; the ransomware makers speaking back to the victims, giving a glimpse into their psychology.
Warning: Confronting.
Seeing the Human Cost of Ransomware
Ransomware variants are similar to biological viruses; they exist in ‘strains’ that rise and fall. They have a limited life span before they become ineffective – and then cyber-criminals have to create a new strain.
This is exactly how the TeslaCrypt virus came to be. After the infamous CryptoLocker virus was taken down in late 2014, ransomware makers weren’t going to let a profit maker die. So they created a variant called TeslaCrypt, or AlphaCrypt, and began spreading it the following year.
The makers demanded 2.5 bitcoins—approximately $550 at the time—from their victims. Alternatively, they could pay $1,000 using PayPal My Cash cards.
But TeslaCrypt was unusual. The makers had set up both a message center and an e-mail address so victims could contact them, acting as “customer support” to help their targets follow through with the payment.
By the end of TeslaCrypt’s rampage in May 2016, it had counted at least 1,231 victims, with 263 interacting with the cybercrime group through their messaging systems. The range of emotions of the victims are vast: from anger, bewilderment, bargaining, to desperation.
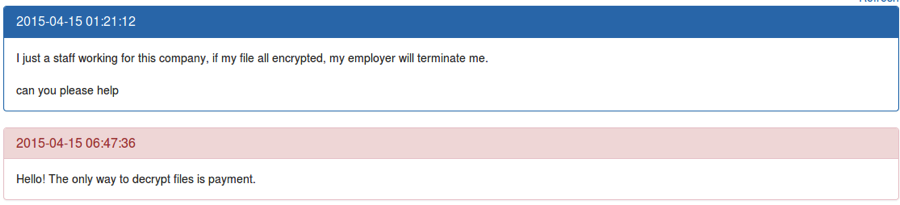
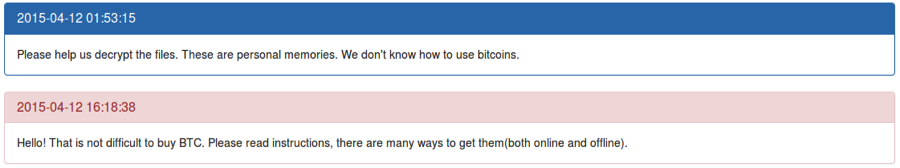
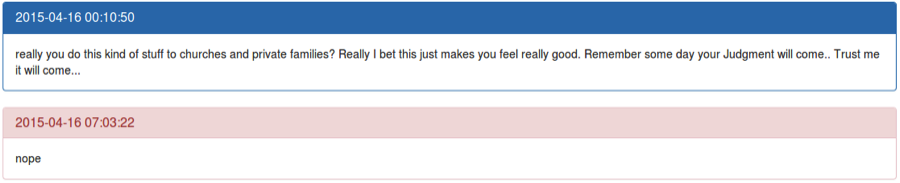
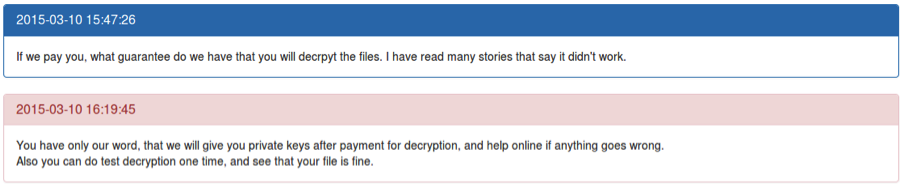
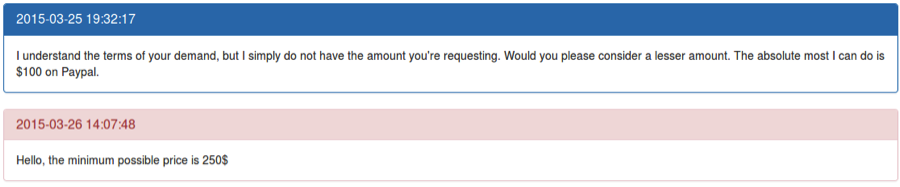
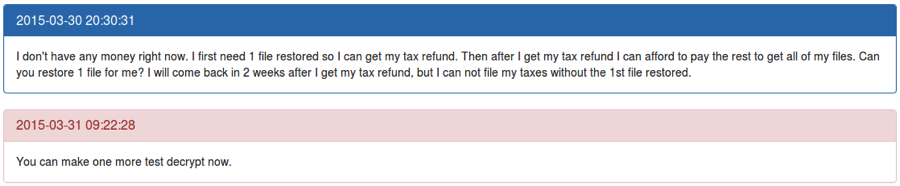
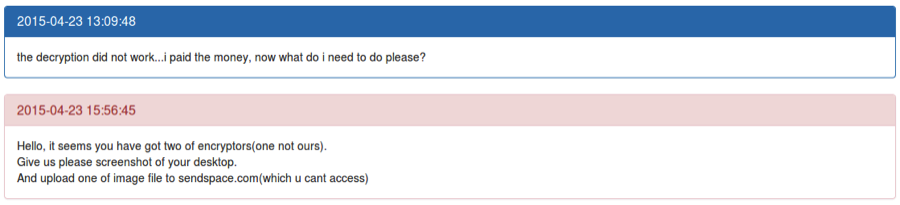
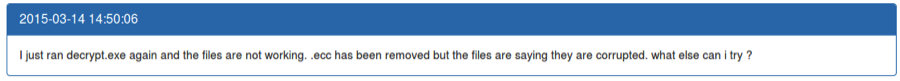
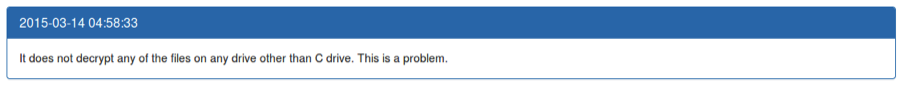
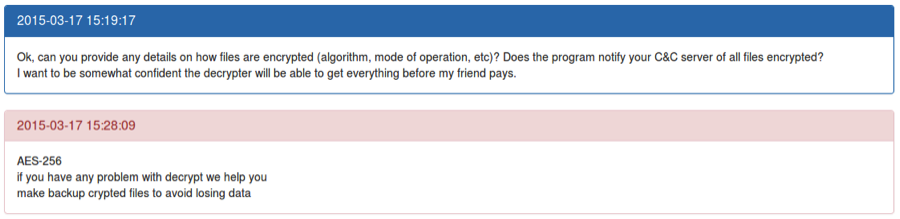
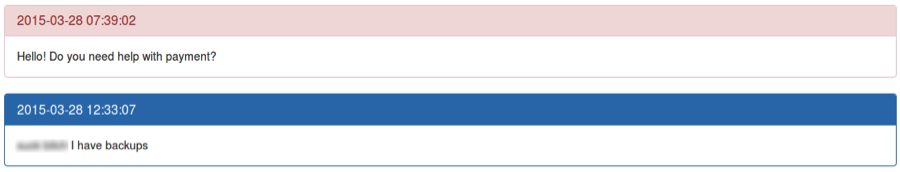
The victims’ comments are in blue; the cybercriminals’ responses appear in red.
In some cases, the attackers agreed to lower their demands, likely not because of empathy but because smaller payments were better than no payments at all.
The minimum cost appeared to shift depending on how much the cyber-criminals seemed to think they could get out of the victim.
In some cases, people had to rely on money coming in from other sources to pay ransom.
In some cases, people paid the ransomware, but could not recover all their files.
The Final Cost: TeslaCrypt Cost More Than WannaCry
The infamous WannaCry virus, which stuck the world this year and brought ransomware into the common conciousness, infected more than 200,000 machines in 150 countries, and earned up to $55,000 before being neutralized.
By comparison, across it’s lifespan, TeslaCrypt hit 1,231 victims and earned $76,522. For ransomware strains, both WannaCry and TeslaCrypt ask for a ransom far below the norm. For instance, the SamSam ransomware (which has mercilessly hit hospitals and 911 services) typically asks for $18k to $28k per victim.
But as the messages show, even a ‘small’ ransom can completely destroy a person’s life (And also a business; see the stats). Which is why it’s so important to backup your data. Ironically, this was the advice the attackers gave to some paying victims before attempting to decrypt their files with their tool.
Whether you’re a home user or a business, backing up your data with an effective backup strategy is the only true way to protect yourself against ransomware. With it, you can recover your data without paying the attackers. And here’s the proof.