We live in a work-from-home (WFH) world. And we were forced into this world rapidly – within weeks, businesses scrambled to adopt WFH in a fight just to stay alive.
The imperative was to “make remote workers productive”. And we’ve been remarkably successful.
But what about making them secure?
You see, cyber-security and cyber-resilience just got a whole lot harder. Instead of one business network to secure, every employee’s home network is a potential cyber vulnerability.
Now that WFH looks likely to be more than just a temporary measure, businesses must mitigate the risks that WFH poses. Let’s look at the issues.
10 second Recap | ||
| RESILIENCE picking yourself up if you get struck down | ||
| VS | ||
| SECURITY Trying to not get struck down in the first place. | ||
Resilience – picking yourself up if you get struck down
Security – trying to not get struck in the first place Every business needs both. You can read more about this in this blog article – the differences between cyber-security and cyber-resilience, and why you need both.
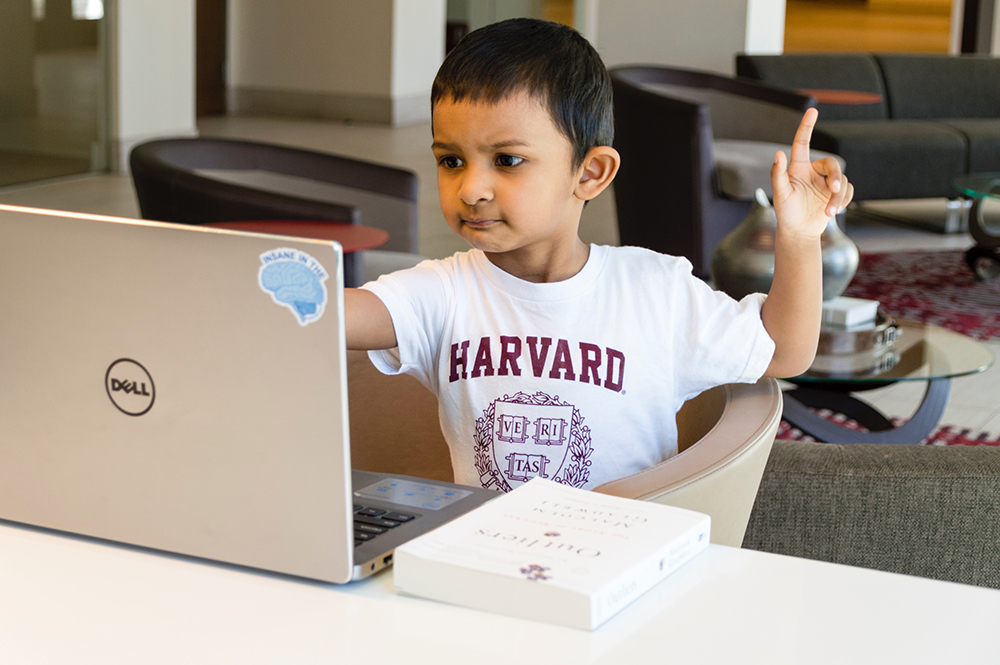
Meet Johnny, your business’s latest weakness
Johnny is the son of Margaret, the business’s marketing manager. Like all 8-year olds, Johnny enjoys online games, and already knows how to visit websites. He even has his own computer!
But did you know that Johnny is now the business’s latest cyber-security weakness? Johnny’s love of online games could easily be his mother’s business’ worst nightmare.
What if:
- Johnny gets lured into clicking on a bright red button that promises access to a new online game, but actually executes a malware bootstrapper instead?
- Malware installs itself silently onto Johnny’s computer. The malware then jumps to other computers on the same network, including Margaret’s WFH computer.
- A few days later, like clockwork, the malware springs to life on all infected computers, encrypting data files – including Margaret’s computer.
- Margaret’s computer is set to sync files to the cloud, so the cloud copies of data get overwritten with encrypted garbage.
- Margaret starts work by booting up her computer, only to find a ransom note.
Employee home cybersecurity – an oxymoron in 5 simple facts.
The reality is that cybersecurity at home will never be as good as at work. Here are five simple facts that illustrate why.
 |
FACT 1 | Employees won’t spend as much on network security, nor will they be configured securely. |
| Do you remember the last time that your business bought a “proper” firewall router? It probably was a major infrastructure investment, costing thousands of dollars for business-grade hardware – from major vendors like Cisco, HP or Dell. What does the average employee use? Most likely, a $50 router provided by the ISP, in the factory default state. With a high probability of weak Wi-Fi passwords and admin consoles secured by credentials of “admin” and “password”, we can safely assume most home networks will be easy to penetrate. |
||
 |
FACT 2 | Employees won’t spend on business-grade AV |
| A basic investment in cyber-security also means that all desktops on an office network are protected by business-grade anti-virus (AV) and anti-malware.
Can the same be said every device on an employee’s home network? AV solutions aren’t going to be cheap. With the highest grade business-grade AV products costing upwards of $5 per month (those with insurance policies) – designed to stop malware and other threats – what does the average employee have? Most likely, free products or nothing at all. |
||
 |
FACT 3 | A business has no control over the clicking habits of employees’ children |
| With so many ransomware and phishing attacks based on social engineering, one hapless click can leave you with major problems.
And while adults get tricked often enough, what about children? All they need is to click on a colorful bright button, promising a free online game, in order to be compromised. Even if children use their own device, malware can spread across a network and infect WFH machines. Suddenly, corporate business risk now depends on whether a child clicks on a malicious button! |
||
 |
FACT 4 | Home networks have more IoT devices |
| Given that IoT devices are notorious for security vulnerabilities, it makes little sense for a business to have “smart devices”. Or if a business does, they are likely to be connected to a separate subnet, away from the main company network.
But what about home environments? Everyday people love to connect IP security cameras, thermostats, lights, smart TVs, smart fridges and toasters to the home WiFi. And almost certainly, those potentially insecure devices will be on the same network as work-from-home computers. |
||
 |
FACT 5 | it’s almost impossible for a business to know the history of employee-owned machines and devices. |
| We know that some WFH environments will have employee-owned machines, whereas others will have company-supplied laptops.
But it’s almost guaranteed that WFH machines will be sharing the same network as personal machines and devices. Let’s talk about the past history of all these personal devices:
On that basis, every employee will have compromised networks! By now, it should be clear that home cyber-security is a major headache for businesses. |
||
So does it really matter? Lessons from COVID-19
It should be clear that home networks and work from home arrangements are a real, present risk for all businesses.
And it should also be clear that ensuring the cyber security of such home networks is going to be extremely difficult.
The answer is surprisingly similar to the COVID-19 situation.
- Do the best you can to try not to catch it. (Easy – follow social distancing guidelines)
- Prepare so that even if you catch it, you can recover and survive. (Hard – make sure you don’t have co-morbidities.)
In the cyber-world, it’s just reversed.
- Do the best you can to not get cyber attacked. (Hard – as we’ve discussed, home cyber-security can be an oxymoron).
- Prepare so even if you get attacked, you can recover.
In my next article, I’ll look at whether backups are truly necessary, and in what circumstances they’ll be useful. Believe it or not, it varies depending on each business’ circumstances, and not every business needs to back up WFH machines. However, for many businesses, it’s certainly a good idea.
Until next time, I wish you good health during these challenging times.
Article 2: When do you need to back up WFH machines?