In a severe lapse of any IT sense, a New York international airport has left its server backups exposed on the open internet—without any password protection—for almost a year.
The internet-connected device contained several image backups for the Stewart International Airport, located 60 miles north of Manhattan, a joint civilian and military thoroughfare. Not only that, the airport frequently accommodates charter flights of high-profile guests and foreign dignitaries.
All this flight information and more were on the equivalent of a public web server, because the airport was backing up unprotected copies of its systems to a Buffalo branded drive, installed by a contract third-party IT specialist.
What Was On The Drive?
You name it, it was on the device. Available for public viewing were hundreds of gigabytes of data, including “confidential” and “sensitive” Homeland Security documents, security plans, screening protocols, human resource files, payroll data, the Airport’s financial tracking database, and staff e-mail accounts.
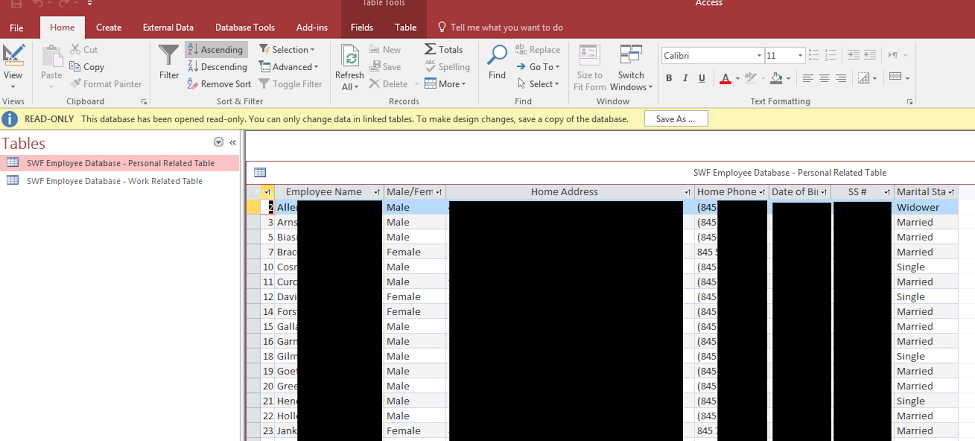
The worst item by far, though, was a list of usernames and passwords for various devices and systems, allowing unfettered access to the airport’s internal network. This let anyone manage passenger records, gates, and boarding through AirIT.
In theory, this information could be used to manipulate boarding passes and other passenger information for international flights—such as giving valid boarding passes to someone on a “no-fly” list, getting a boarding pass to any destination, and knowing who is going where and when.
In a stroke of sheer luck, no hackers used the publicly exposed passwords to shut down airport operations—something that could have easily been done with the openly accessible backups.
How Did It Even Happen?

According to Chris Vickery, lead security researcher of the MacKeeper Security Center, the problem was potentially caused by two issues. The first was the airport had been experimenting with a backup software. The second was handing one gigantic task to a single external consultant.
“I was informed (by Airport IT staff) that part of the process involved opening port 873 on the firewall and that the ShadowStream service, part of ShadowProtect, may have been utilizing some aspect of the remote synchronization service (rsync),” Mr Vickery said.
“The current working theory is that these two factors aligned and resulted in a breach scenario. But all of this begs the question: Would such an oversight happen if AvPORTS employed even one full-time IT guy at Stewart?
“This is a classic example of what can go wrong with privatization. For-profit companies have every incentive to, all too often, prioritize revenue over best practices.”
Scandalous Information From The Leaks
With the backups on the internet, the press have quickly seized several scandalous documents. Many of these catalog serous security failings over the past few years.
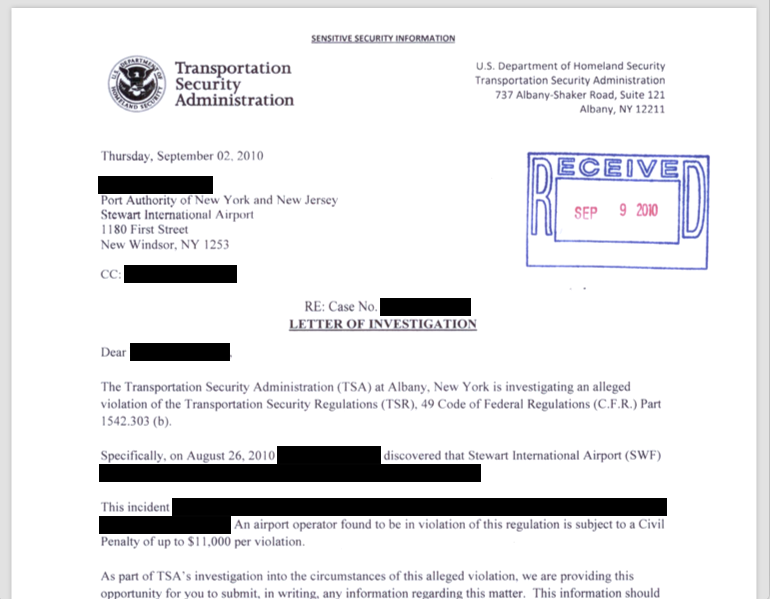
For instance, in 2010, the Airport staff were unable to screen names against the US government’s watchlist of suspected terrorists for an unknown period of time. Since the Airport had no access to the list, they were unable to check their passengers against it.
Other security slip-ups include not properly checking counterfeit badges, unsecured baggage carousel keys (which gives direct access to the airport’s secure area) left on ticket counters, unsupervised access to non-cleared visitors to sensitive and restricted areas, and 15 Transport Security Administration (TSA) investigations.
According to security researchers who investigated the Airport’s password system, the duplication of passwords meant someone who had guessed or found out a password for one system could use it for another.
A spokesperson for Port Authority, who owns the airport, said in a ZDNet article they were investigating the “leak”. However, they “don’t believe” the backup file contained customer passage data.
The investigation will reveal if there are any ongoing risks or vulnerabilities to the agency’s data, they said.
Who Downloaded It, and What Now?
It’s uncertain, but the first thing Port Authority would want to do is review historical traffic patterns from the internet to the backup server. This will let them determine if any massive downloads took place. And not only do they need to hold the contractors accountable, they need to investigate the management that lead to such a catastrophic slip-up in the first place.
Backups are vital, but properly handling them is even more so. Make sure your backups are not stored on an internet-connected device, they have a password, and are highly encrypted—no matter the size of your business. Also, triple check that you’re not leaving a port open!
BackupAssist is the #1 Backup and Disaster Recovery software for Windows Servers. It gives you the power to securely protect your backups with AES-256 Encryption, password locking, two-stage verification with a USB key, and more. Read more about it, or download the free 30-day trial today.






