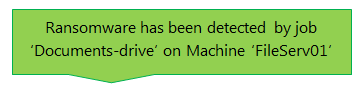
You’re sitting at home on Wednesday night watching TV when your phone buzzes and a flashing light appears. It looks like someone’s sent you a message. You reach over and open your text app to see something odd. It’s a text message from BCKUPASSIST – your company’s backup software has sent you a text. You sit back and open the message– then start to feel sick as you read it.
You stare at the phone as the weight of the message sinks in. Has your company been hit by ransomware? Has the ransomware spread? Is the company able to function? Is there really an infection?
This is a moment you really want to have planned for. If you have not, the best way to start is by reading this article and our CryptoSafeGuard user guide.
Do you really have a ransomware infection?
It depends. CryptoSafeGuard looks for signs of ransomware. This means it looks for changes in the files being backed up to see if they have characteristics that are often associated with ransomware.
If this is the FIRST time your backup job has run with CryptoSafeGuard, it’s possible that some of the files being backed up have characteristics often found in ransomware encrypted files (like suspicious file names), and CryptoSafeGuard has therefore sent a warning. The backup jobs will not be blocked as you are within CryptoSafeGuard’s grace period. The grace period for a job lasts until the job has 3 consecutive clean scans.
If this is not the first time you’ve run the job, then this alert means something has changed in the files since the last time you ran the backup, and this change was suspicious enough to trigger a ransomware alert.
In both scenarios, you still need to be careful and investigate the files that triggered the alert.
Note: To avoid a ‘false positive’ CryptoSafeGuard alert occurring at night when you are at home, you should manually run the job while you’re available. This means you will be able to respond immediately and whitelist any files if required.
What to do next
You’re at home. The server’s at work. So what do you do? Do you call the boss? Do you go into the office? Again, you need to plan this in advance and document the process, just as you do with your disaster recovery process.
Ultimately, you will need to leave the comfort of the couch and log into the machine with the installation of BackupAssist that generated the alert. This means either opening a remote session to that machine, or going into the office and logging onto that machine locally. Only then, can you open BackupAssist, respond to the alert and browse the local folders if required.
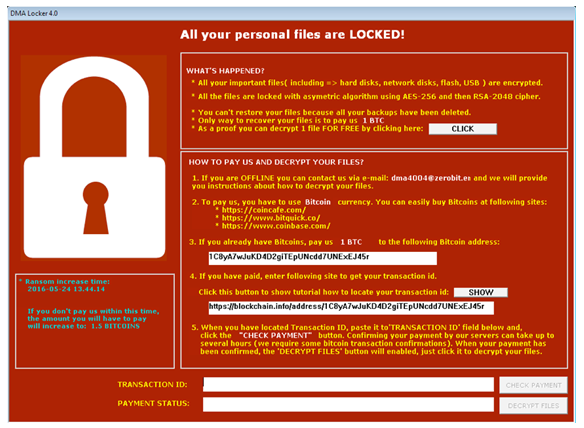
Determining if you have a ransomware infection
If you have a ransomware infection, it may be obvious when you log into the machine because when the ransomware has finished encrypting your files, it will display a message informing you that your files have been encrypted and how to pay the ransom. If you see such a message, you will know that that CryptoSafeGuard alert was genuine and that you have been infected.
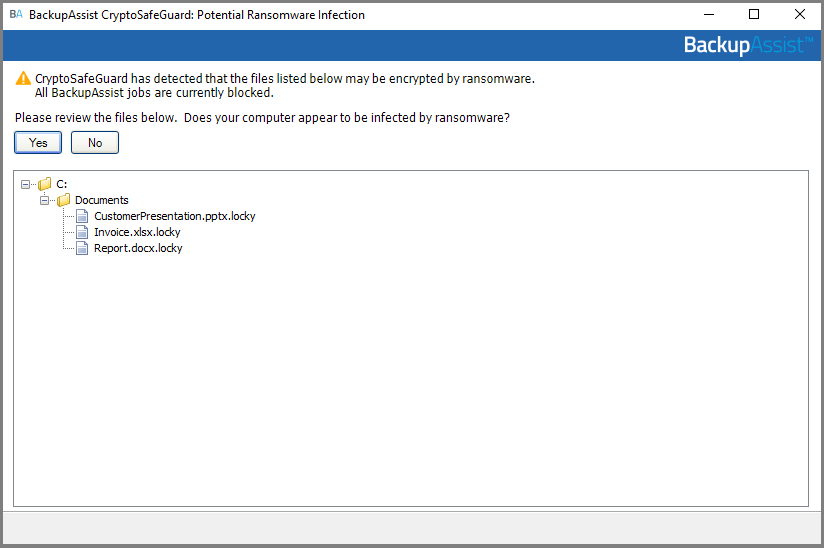
If you log in and there is no ransomware notification, it is still possible that you have been infected but the encryption process has not finished or the ransomware was not able to complete its infection process. You will therefore need to use CryptoSafeGuard UI to view the files that triggered the alert, and determine if they were infected or if it was a false alert. The UI will display the files and can be used to open the folder containing those files in Windows.
What to look for:
- Has the file’s name been changed?
- Is the file that caused the alert new? Some ransomware infections will add a ransomware note file.
- Can you open the files? Some encrypted files cannot be opened and don’t show a file association.
- If you can open the file, what does it look like? If an infected file can be opened in notepad, it may show illegible text because it is encrypted.
If CryptoSafeGuard does not show any files to review, then this may be a new strain of ransomware. In this case, check files commonly targeted by ransomware such as files on your desktop, your documents, the Documents folder, the Pictures folder etc. and check for signs of infection as using the ‘What to look for’ points shown above.
How to respond to the ransomware alert
The purpose of this article is to pose the questions you may be faced with in a ransomware scenario and highlight the importance of being prepared. How to use and administer CryptoSafeGuard is documented in our CryptoSafeGuard user guide. You will need to read this guide to properly understand how to configure CryptoSafeGuard and how to respond to CryptoSafeGuard alerts. Below is an overview of the process.
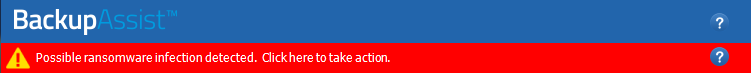
Open BackupAssist and respond to the alert using the CryptoSafeGuard UI as follows:
- Confirm that there is an infection. BackupAssist’s jobs will remain blocked to protect your backups.
or
- Confirm there is no infection, and take one or more of the following actions:
- Whitelist the files that caused the alert. This is performed within the CryptoSafeGuard dialog.
- Delete the files that caused the alert if you do not need them and want to remove them. Files are deleted by right-clicking the file/folder, opening it in Windows and deleting it from there.
Note: In some circumstances, CryptoSafeGuard may only ask if you have an infection or not, and not list any files. In this case, check files commonly targeted by ransomware such as files on your desktop, your documents, the Documents folder, the Pictures folder etc. and check for signs of infection as using the points in the ‘What to look for’ section above.
If you have a ransomware infection
The purpose of CryptoSafeGuard is to shield your backups from ransomware so that an infection cannot spread to them, and to stop BackupAssist from backing up infected files. If you have a ransomware infection, recovering from it should be as straight forward as performing a recovery using those backups.
Your documented recovery process should be followed and your systems brought back online. However, to do this means you must, as always, follow the fundamentals of any backup strategy.
These fundamentals include:
- Having System Protection bare–metal backups, as only these backups can be used in a recovery. To learn more, see our System Protection backup guide.
- Regularly test your recovery process so that it runs as expected. This process should be documented, tested and those involved aware of their tasks and how to perform them. To learn more, see our planning for a recovery article, and infographic.
- Know your Recovery Time Objective. This means your business knows and agrees with how long the recovery process will take. To learn more, see our RTO RPO article.
- Know your Recovery Point Objective. This means knowing how old your backup can be for your business to be able to resume its operations after a recovery. To learn more, see our RTO RPO article.
Being prepared for ransomware
Being prepared for ransomware is now an important part of systems administration. Antivirus / malware software is your first line of defense against infection and may be able to detect and stop a ransomware infection. However, ransomware is evolving and in many instances it encrypts files on machines and spreads to other machines, in spite of antivirus software.
This means performing a recovery is the only sure way to remove a ransomware infection, and to perform a recovery you need uninfected backups. For this reason, BackupAssist’s CryptoSafeGuard runs every time your backup jobs do to make sure your backups are safe if you need to recover from ransomware. So check that you have CryptoSafeGuard enabled and understand how it works.
CryptoSafeGuard is available to all BackupAssist users who have BackupAssist 10.1 or later and active BackupCare.
Not sure if your BackupCare has expired, or sure that it has? Find out here. You can use the same link to renew your expired BackupCare. To upgrade to BackupAssist 10.1, click here and go to the Upgrade/Update tab.