WiFi is everywhere, and so are the security problems
According to industry research from Cisco, in 2021 over 50% of all internet traffic will be over WiFi. WiFi is everywhere, used by everyone and every organisation, from staff using iPads and laptops to industrial control systems on manufacturing lines. And if WiFi is everywhere, so too is WiFi hacking.
Organisations handling sensitive data are obligated to check for unknown or unauthorised WiFi, as it could be set up to attack or hijack their WiFi networks. This is a very real problem, as an attack could allow criminals to steal credentials to infiltrate corporate systems or stop WiFi from working altogether. For example, organisations processing or storing debit or credit card transactions need to comply with the PCI-DSS (Payment Card Industry Data Security Standard), which requires them to do a quarterly audit of their premises to look for unauthorised WiFi and remove it.
As recently reported in the AFR, during a WiFi audit we did with a large financial organization in Australia, we found an unknown WiFi device hidden under the floor and a device in a gym bag which was switched off remotely when we approached. This was a huge surprise as their own audits hadn’t picked these devices up.
What most people don’t know is that all WiFi has vulnerabilities that can be exploited – even the most heavily protected corporate networks – and how would you know if you were being attacked?
Common attacks in WiFi hacking
WiFi hacking can take several forms. These are just a few attack methods commonly used:
Deauthentication Attacks
Disabling networks using deauthentication attacks – These attacks exploit a known weakness in the protocol and can be generated on standard PC equipment or using cheap devices available online for a few dollars. When activated, all WiFi devices will be disconnected from the network and will be unable to reconnect until the attack stops. High end routers provide protection against this type of attack, however, the standard WiFi routers installed in most homes and businesses are vulnerable.
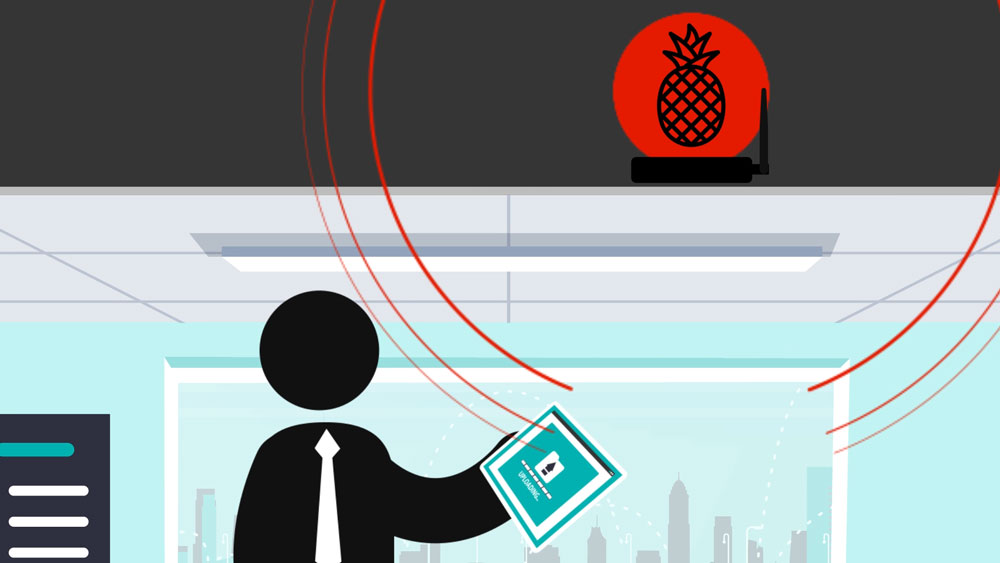
Evil Twin attacks
Man in the Middle and Evil Twin attacks – These attacks use fake access points to trick WiFi devices to connect to them instead of the real network. How can you be sure you are connecting to the genuine access point? The scary part is this can be done automatically with devices such as the WiFi Pineapple without the user even being aware. For example, most people have their mobile phones set to automatically connect to their home or work network, or even the local StarBucks or airport lounge. Their phones continuously send out probe requests’ every 10 seconds or so looking for these networks which the attacker can intercept and use to generate a fake access point. When the phone finds a network of the same name and credentials (fake or not) within the vicinity they automatically connect and the attacker can gain full network control. Strongly protected corporate networks cannot prevent this as the attack occurs on the user device, not the corporate network. Even the latest WPA3 standards do not solve this issue.
Spying on WiFi
Eavesdropping and capturing transmissions – leaking of data from organisations is a serious concern and can occur with unauthorized hot spotting of phones or simple eavesdropping of WiFi transmissions. Most organisations do not realise how vulnerable they are, often believing they are protected by WPA2 encryption or use of TLS/SSL encrypted web communications. An attacker can capture and store transmissions for extended periods then use password cracking techniques to get the WiFi password and decrypt all transmissions as far back as they like. Using a strong password provides reasonable protection, assuming it’s not commonly known, however, modern cracking techniques are making this task much easier and can easily exploit most common passwords used today. I often hear IT experts claim that we use SSL so frequently today, we need not worry about eavesdropping, however, not all traffic uses SSL. I am yet to find an organization that is using SSL on their printers for example. In other words, any document sent to the printer via WiFi can be captured in clear text.
Take action and secure your WiFi from hacking
A recent case in Melbourne highlighted this issue when a stock broking firm was suspected of insider trading due to suspicious share trades being made prior to official announcements. An investigation revealed a person in a parked car outside the office that had hacked the WiFi and was obtaining data prior to publication. They have since been jailed.
Don’t panic! There are some basic low-cost measures that can be implemented to reduce risks which we are happy to share, but they are not a panacea. If you have access to sensitive data or systems over WiFi, you need to take WiFi security seriously.
Stay tuned for the next article in this series…
About the Author:
Mike Thompson is the co-founder and CTO of HackHunter, an Australian cyber security company making sure WiFi is used for good.
HackHunter provides real-time visibility of the corporate WiFi network environment, detects unauthorised WiFi, alerts if it is malicious and locates the source with precision, to within a few centimetres.
Mike is an IoT expert and has over 25 years’ experience in information and cyber security. He has been a CISO for an insurance company and security consultant to over 50 organisations including NAB, Telstra and the Privacy Commission.