Millions of Office 365 users were recently struck with malicious malware that bypassed Microsoft’s built-in security and devastated their systems.
Almost as unnerving as malware smashing so easily through Microsoft safeguards was the fact that once infected, the ransomware speaks to the user directly through their speakers.
Unlike other ransomware, Cerber plays an audio file to inform users of the infection—while showing a written note at the same time.
The phishing attack started on June 22 2016 and lasted for more than 24 hours, according to cloud-security firm Avanan. It said during the span of the attack, around 57 percent of users “received at least one copy of the malware into one of their corporate mailboxes.”
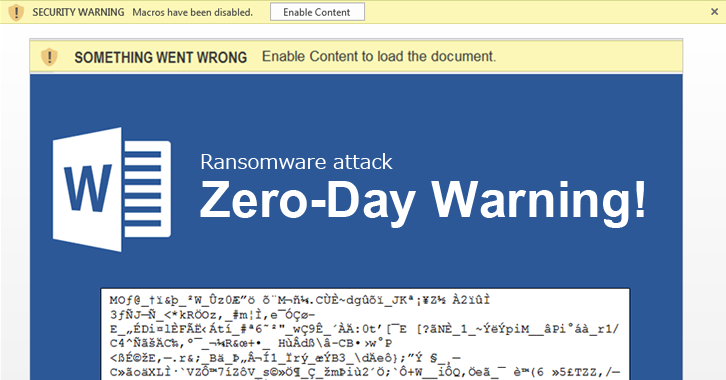
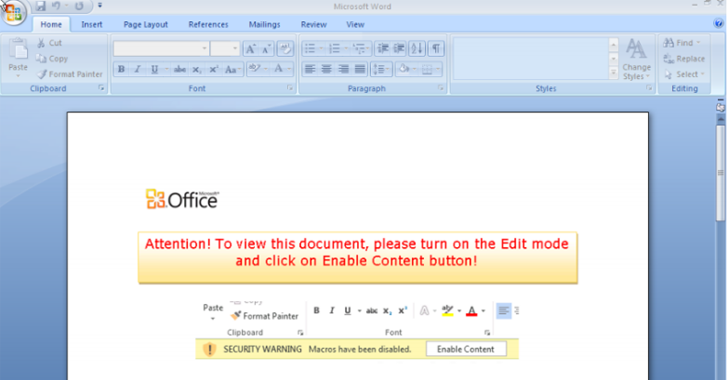
Avanan said the virus targeted Office 365 users specifically, trying to trick them into activating macros to let the malware in.
The Cerber ransomware first reared it’s ugly head back in March, and has since been worked on and upgraded by malware makers. Cerber has been used in campaigns targeting the United States, Turkey, the United Kingdom, Germany and Australia, as well as in DDoS attacks.
As if the malware couldn’t get any creepier with its built-in voice, Cerber ransomware was witnessed morphing every 15 seconds in early June. This ability gave it the ability to evade detection by switching its hash repeatedly.
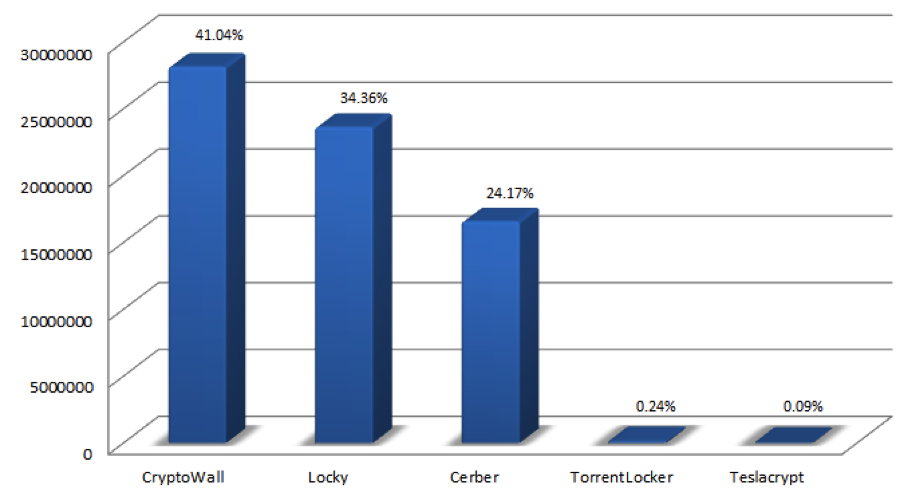
This constant work has seen Cerber rise in rank to be considered the third largest ransomware threat, behind CryptoWall and Locky. Cerber enjoys a 24 percent Ransomware market share, behind CryptoWall (41 percent) and Locky (34 percent).
A number of the world’s top IT security experts urged businesses to take proper precautions following the Office 365 attacks and to make sure to take proper precautions.
Here are the precautions IT experts recommend you take against Cerber:
- Always keep your system and antivirus up-to-date.
- Disable Macros in your MS Office programs.
- Regularly backup your files in an external hard drive. Use a reliable backup program like BackupAssist that can encrypt your data and also perform offsite backups. Performing the 3-2-1 rule of backups is essential.
- Perform regular test restores of your data to make sure they’re ready for if you’re hit with malware (or any other data emergency).
- Beware of phishing e-mails, spams, and clicking the malicious attachment.
- You can use an Intrusion Detection System (IDS) to quickly detect malware and other threats in your network. This, combined with a strong backup strategy, has allowed companies to thwart new malware in the past and avoid paying ransoms.
If you’re not already backed up, we recommend downloading the 30-day fully featured trial of BackupAssist and then seeking out a reliable IDS for your servers.