If you’re familiar with Ransomware, you know its organized crime. Hackers target your precious data, encrypting and locking it behind a passkey only they have. You pay the ransom, you get the key and your data back.
Usually, it’s in the hacker’s best interest to follow through. They don’t want word to get around that they don’t return your data. It’s bad for business; and that’s what it is, a business.
However, the latest ransomware on the block, ‘Petya’, flies in the face of this concept. Not only is it more malicious than all the crypto-extortion programs before it, it sometimes doesn’t even help to pay.
Here’s how Petya traditionally works:
A Trojan CV
The standard infection scenario currently looks like this; you or one of your staff receives an e-mail pretending to be a job application. The e-mail contains a Dropbox link to a zip file which pretends to be their resume, typically containing:
- A photo of a young man claiming to be an applicant. In fact, this is a common stock image.
- A fake resume that is really a malicious EXE, either in a self-extracting archive or fake PDF file.
When you click on the CV, you receive a Blue Screen of Death instead. That’s all it takes to start Petya’s ball rolling.
A Pop-Up Alert
Petya doesn’t even attempt to bypass your user account control (UAC) and get your Administrator privileges. You’ll receive this pop-up alert instead:
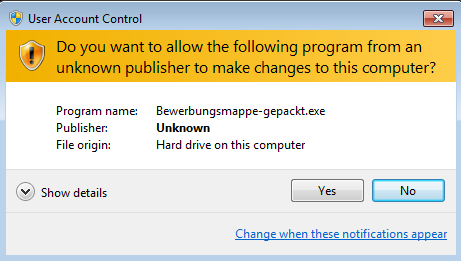
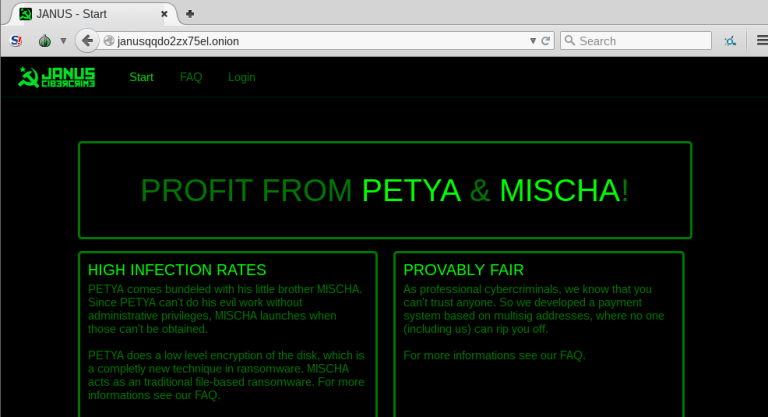
In the past, if you hit ‘no’, the Petya infection would stop its infection routine. But Petya is evolving. Now, if you hit no it installs another ransomware program, dubbed ‘Mischa’, which begins to encrypt your files directly in an operation that doesn’t require special privileges. There is currently no way to restore files encrypted by Mischa without paying the ransom.
So you’re damned if you do, damned if you don’t.
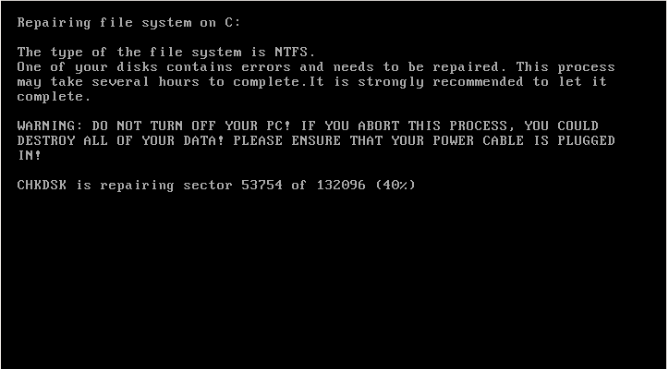
Let’s say you hit ‘Yes’, and end up running Petya instead of its less-sophisticated cousin, Mischa. When you do, the the system crashes. When it restarts, Petya puts up the following screen, pretending to be running a CHKDSK scan:
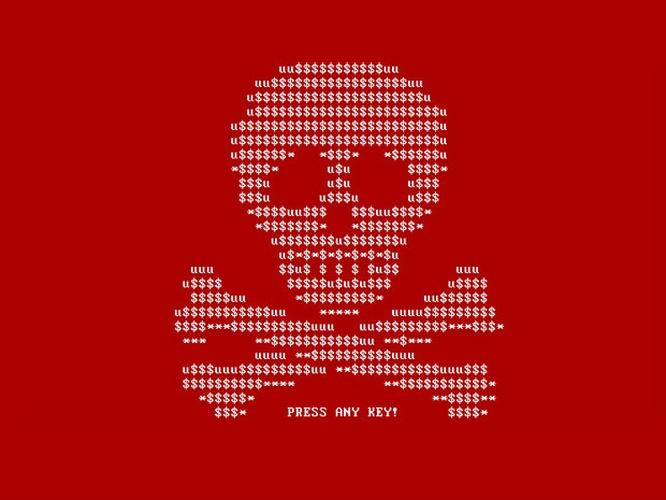
Don’t be fooled; this is Petya’s attempt to buy time as it’s already encrypting your data, trying to trick you into not pulling the plug on your machine. If you’re unfortunate enough to let it run to completion, you’ll be greeted with a blinking screen with this ASCII art:
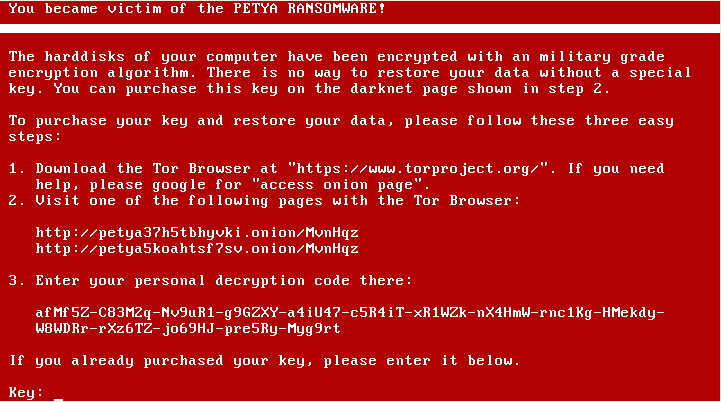
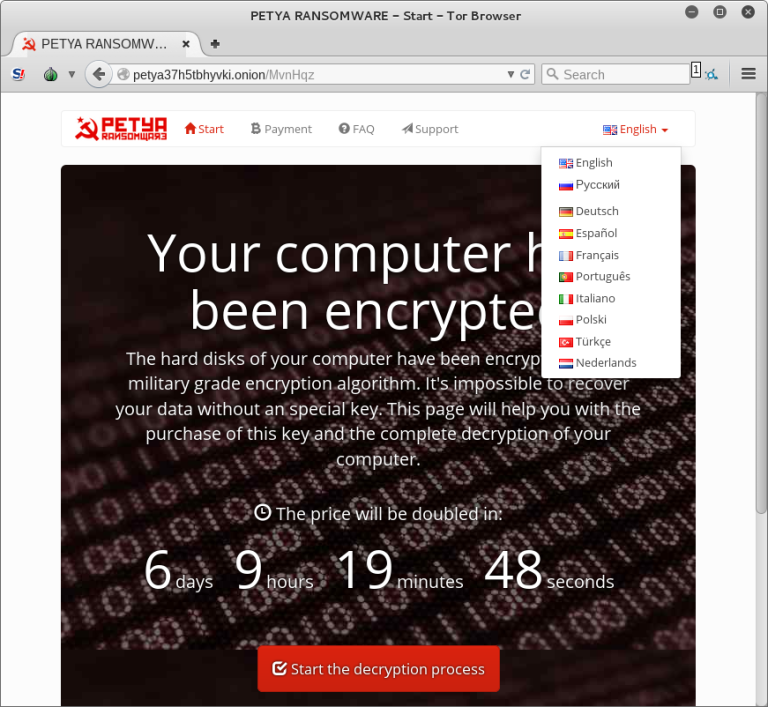
Pressing any key after this leads to the main screen with the ransom note, the information necessary to reach the web panel and proceed with the payment:
Currently Petya asks for around 0.99 bitcoins and Mischa asks for 1.93—that’s around US $430 and $875 respectively. Why you have to pay twice as much for Mischa is anyone’s guess.
What makes it different?
Petya’s infection method isn’t new. What is new is how it goes about it. Common ransomware usually encrypts certain kinds of files—pictures, office documents, etc—and leaves your operating system unharmed so you can pay the ransom.
Not so with Petya. Instead, it blocks access to your entire hard drive, infecting your Master Boot Record (MBR). In layman’s terms, your MBR is what runs before an operating system like Windows, and by doing this it ensures it gets to run its malicious code first.
Worse news? It does this completely offline. That means you can’t unplug your internet and hope to halt the process. In fact, you’ve got to find another computer in order to pay the ransom and get your data back.
That’s an incredibly odd move, like kidnapping a family member but also your car keys. In the end, it’s just going to make it that much harder to get the ransom money.
Even if you pay, your data may be lost
To pay the ransom, you’ll need to head to the ‘Dark Web’, the seedy underbelly of the regular internet. There, you have to pay them in Bitcoins, which is the favoured currency of the web’s black market.
The really bad news is, the decryption process is likely to catastrophically fail. The reason is the malware makes incorrect assumptions about the layout of your disk. That means the malware can’t unscramble your data.
Given the abysmal rate of data recovery software at recovering your data, that may mean it’s gone permanently with the single click of a CV attachment.
Prevention is the best cure
If you’ve lost your data, you can pay the ransom and hope the decryption works, try your hand at recovering it, or wait until proper countermeasures and decryption tools are made by software security giants. But none of these are sure things, and all of them take time and money. And you can expect to see a lot more of Petya and Mischa, since they’re now even being offered as Ransomware-As-A-Service:
The best solution by far is prevention, whether it’s before you’ve been hit or after. Having regular backups means that your data isn’t lost, and performing a bare-metal restore of your hard disk. A restore isn’t possible, since you’ll need to fully format your drive in order to purge the virus.
Using a reliable backup solution like BackupAssist along with a proper backup strategy (E.g. The 3-2-1 Backup Rule) means you don’t need to pay hackers if you’re hit with ransomware, or any other data disaster. Pairing this with an effective anti-virus solution is your best bet against malware.