It’s 4.55 PM on a Friday afternoon. You’re just about to clock off and go have a hard-earned beer, when a user calls your IT help-desk saying he can’t access any of his files and keeps getting a pop-up message that won’t go away. Already, your blood is starting to run cold, but just as you get up to check it out the phone rings again – another user can’t access her files either. Yep, you guessed it. Cryptowall. And it’s spreading fast across the network.
Ransomware is an IT professional’s worst nightmare, and it’s happening to you. What do you do now?
If You’re Not Prepared, The FBI Says You May Have to Pay

We’ve written about ransomware before, but as a quick refresher, it can be defined as any malicious software application that prevents access (usually by encryption) to critical data on an infected system until a ransom is paid.
As the independent news outlet, The Security Ledger, recently reported: some FBI agents’ advice to businesses and individuals hit by ransomware is often just to pay the ransom, should a victim not have the means in place to recover to a point before the attack occurred. This controversial statement was made by Joseph Bonavolonta, Assistant Special Agent in Charge of the CYBER and Counterintelligence program for the FBI’s Boston office, at the Cyber Security Summit 2015 in Boston.
“The ransomware is that good,” said Bonavolonta. “To be honest, we often advise people just to pay the ransom.”
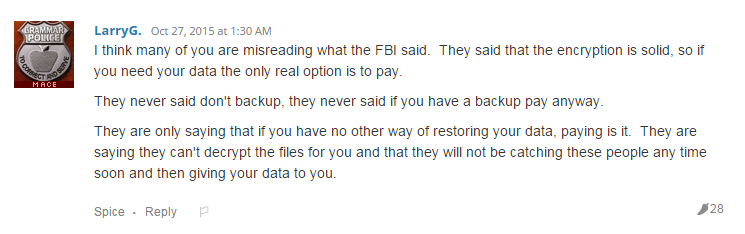
Understandably, this caused a lot of consternation and even outright anger among IT professionals when the news was posted to a Spiceworks discussion last week, with many feeling it a tacit admission that the criminals have won when it comes to ransomware. However others were quick to point out that once ransomware has infected a system that doesn’t have effective backups in place, there’s really nothing the FBI or anyone else can do to get that data back. That doesn’t mean the FBI won’t pursue and perhaps ultimately catch those responsible, but that could be a long way down the road and won’t help retrieve data that companies need back as soon as possible to remain operational.
Having said that, while paying a ransom may be the only way to get the data back if you don’t have backups, this is directly funding criminal enterprises and must be avoided at all costs. Luckily, for the properly prepared there’s always one sure-fire way to retrieve encrypted data and avoid paying the ransom: recover from a backup taken before that data was ever encrypted.
The IT professional in the hypothetical we started with had better hope s/he has a best-practice backup strategy in place!
Backups: The Best Defense Against Ransomware

Let’s revisit our hypothetical scenario. You’ve just discovered a ransomware infection that’s spreading across your network, and now you’re wondering what to do next. Well, actually, no you’re not. Because you’re an IT professional and that means you have backups. Backups that you’ve regularly tested and know will recover without a problem. And therefore your next steps are both obvious and straight forward.
First you take the network offline to prevent the infection spreading to anywhere it hasn’t already worked its malicious tendrils into. Next, you identify exactly when the infection occurred – or as close as possible. Finally, you simply recover all of the affected systems from the most recent backup before the infection took hold. Done and done. Data retrieved, business continued, and no criminal paid.
We’ll even throw another step into the mix to really minimize any downtime – if you’re running a Hyper-V environment, you’ll use something like BackupAssist’s Rapid VM Recovery feature to spin up Hyper-V guests from their backup destination before you recover in full. This will mean you can recover systems in seconds, and then perform a full recovery later at a time more convenient to business operations.
Bottom line? Ransomware happens. Scarily often, and with seemingly exponential frequency as each year passes. You don’t want to pay the criminals to get your data back. You just don’t. So that means properly backing up your servers, systems and networks is not only common sense, it’s arguably your civic duty.
The FBI’s advice to many people who don’t have backups may be to pay the ransom – but our advice is have backups to begin with and don’t be put in that situation!
What’s your take on the FBI’s advice? Does it encourage criminals or just reflect reality?
Leave your thoughts in the comments, tweet @BackupAssist or post to facebook.
Share this article, because ransomware is serious.
2 thoughts on “Ransomware – FBI Says Play Safe or Pay Up”