What is CryptoSafeGuard? A Quick Summary.
CryptoSafeGuard consists of two distinct components that protect your backups from ransomware.
- The CryptoSafeGuard Detector, which prevents infected files from being backed up.
- The CryptoSafeGuard Shield, which protects your existing backups from ransomware.
This article looks at how to set up CryptoSafeGuard so that you get the best results from these two components.
Adding CryptoSafeGuard
CryptoSafeGuard is available for all BackupAssist users who have BackupAssist 10.1 or later and an active BackupCare subscription.
Not sure if your BackupCare has expired? Click here to check and/or renew your subscription. To upgrade to BackupAssist 10.1, click here and go to the Upgrade/Update tab.
Enabling CryptoSafeGuard
The next thing to do is check that you have CryptoSafeGuard is enabled.
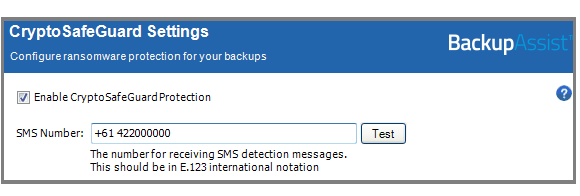
To check and enable CryptoSafeGuard:
- Open BackupAssist.
- Select the Settings tab.
- Select CryptoSafeGuard.
- Check that there is a tick by Enable CryptoSafeGuard protection. Tick the box if it is not ticked.
NOTE: If the tick box is greyed out, it means that you do not have an active BackupCare subscription.
CryptoSafeGuard will show as enabled on your Backup tab’s Home screen (As shown below).
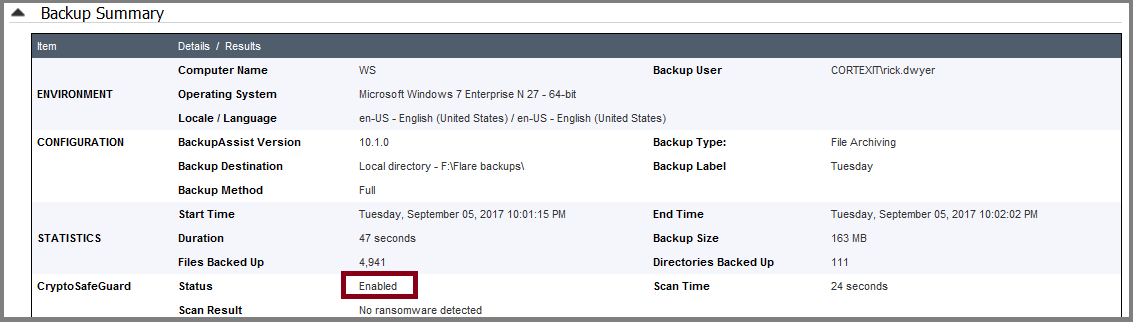
CryptoSafeGuard will also show as enabled in your backup reports.
Setting up notifications
With CryptoSafeGuard added and enabled, you now need to enable SMS notifications. These notifications send an alert to a mobile number if CryptoSafeGuard detects a possible ransomware infection. Set up SMS notifications in the same dialog used to enable CryptoSafeGuard. As you can see in the Settings screen shot above, all you need to do is enter the phone number into the field provided.
Type the phone number in the SMS Number field using the standard international phone number format “+<country code><mobile phone number>”. The SMS test button will become active once a phone number has been entered in the correct format.
Click Test and a test message will be sent to that phone.
If you have set up the Email server settings and Email address list, and enabled Notifications in the backup job, the emailed backup report will also inform you of a possible ransomware detection.
Securing your backup destination
The CryptoSafeGuard Shield protects your backups from ransomware by only allowing BackupAssist to create, delete or update data in your backups. This means if the BackupAssist machine is infected, the ransomware cannot corrupt or delete your backups. However, if the backups are on a NAS or network share, you need to ensure that all other computers cannot access your backup destination, as they could potentially spread an infection to it.
Important: Only your BackupAssist computer should have access to the folder containing your backups.
To ensure that this is the case, you should use Windows permissions to restrict access to the folder containing your backups. Ideally, only the Backup User Identity (the Windows account used to run your BackupAssist) should be able to access your backups. So take the time to check that only machines running BackupAssist and CryptoSafeGuard have access to the folders that the backups are in, and those folders only allow access to the Backup User Identity.
Test CryptoSafeGuard with your backup jobs
CryptoSafeGuard runs when each backup job starts and checks the files you’re backing up to see if they exhibit characteristics commonly associated with files encrypted by ransomware. For example, mangled file names or malformed files. It also checks for the mathematical properties of encrypted files. The process errs on the side of caution, so CryptoSafeGuard may raise alerts for files that are not infected.
This is more likely to occur the first time you run a backup job with CryptoSafeGuard. For this reason, you should do a test run of the backup jobs to see if any safe files are flagged by CryptoSafeGuard – so you can whitelist them.
See our CryptoSafeGuard guide to learn how to review and whitelist files.
What next?
CryptoSafeGuard detects signs of a ransomware infection and protects your backups from being impacted by a ransomware infection. It does not protect the actual system from ransomware, or remove ransomware. If a machine’s files have been encrypted by ransomware, that machine will usually need to be recovered from a backup, which is why CryptoSafeGuard is such a valuable feature.
To make sure CryptoSafeGuard and your backups continue to function as intended, remember to check your backup reports, test your disaster recovery plan and run test restores and recoveries.
This article provides an overview of the set up process, but you should also read the CryptoSafeGuard guide. For further reading, see our article on How to respond to an alert.